Multi-Branch Corporate VPN
Secure Site-to-Site IPSec Architecture with High Availability and Traffic Optimization
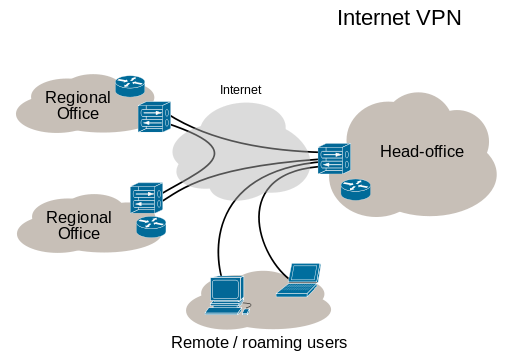
As organizations expand across geographic regions, maintaining secure and reliable communication between branch offices becomes critical. This case study outlines how a fragmented, unsecured inter-branch network was transformed into a centralized, encrypted, and highly available enterprise VPN infrastructure.
Client Background
The client operates multiple branch offices that depend on centralized ERP systems, VoIP communication, financial applications, and shared storage hosted at the main data center. As the number of branches increased, connectivity instability and security risks began affecting daily operations.
Primary Challenges Identified
- Unencrypted traffic between branch locations
- Frequent latency spikes impacting VoIP and ERP
- Single firewall per location with no failover
- No centralized management of firewall rules
- Manual recovery during ISP outages
Strategic Network Design
A structured architecture was designed focusing on encryption, redundancy, segmentation, and performance stability.
- Full IPSec encryption (AES-256, SHA-256)
- High Availability firewall clustering (CARP)
- Dual WAN failover configuration
- VLAN segmentation for traffic isolation
- QoS prioritization for business-critical services
- Centralized monitoring and alerting
Solution Implementation
1. IPSec Site-to-Site VPN Deployment
Secure tunnels were established between headquarters and all branches using strong encryption standards and Perfect Forward Secrecy. Phase 1 and Phase 2 parameters were standardized for consistency and scalability.
2. High Availability Firewall Cluster
At headquarters, pfSense firewalls were deployed in an active-passive CARP configuration. State synchronization ensured uninterrupted traffic during failover events.
3. Dual ISP Failover
Each branch was configured with two WAN connections. Gateway monitoring automatically rerouted traffic if primary links degraded or failed.
4. VLAN Segmentation
- Corporate user network
- VoIP network
- Server infrastructure
- Guest network
- Management interfaces
This minimized lateral movement risks and improved broadcast control.
5. QoS Traffic Prioritization
Latency-sensitive applications such as VoIP and ERP were prioritized using traffic shaping policies. This eliminated jitter and packet loss during peak hours.
Performance Comparison
| Metric | Before Implementation | After Implementation |
|---|---|---|
| Inter-Branch Encryption | None | Fully Encrypted IPSec |
| Firewall Redundancy | Single Device | HA Cluster (CARP) |
| VoIP Stability | Frequent Jitter | Stable Low Latency |
| Failover Response | Manual Intervention | Automatic Instant Failover |
| Branch Onboarding | Custom Manual Setup | Standardized Template Deployment |
Business Impact
- Secure encrypted communication between all branches
- Improved VoIP clarity and ERP responsiveness
- Elimination of single points of failure
- Reduced downtime during ISP disruptions
- Simplified onboarding for new branch offices
- Stronger security posture aligned with enterprise standards
Long-Term Scalability
The architecture was designed with future growth in mind. New branches can now be integrated quickly using predefined firewall templates and standardized IPSec configurations. Centralized monitoring ensures ongoing performance and security compliance.
Conclusion
By implementing encrypted IPSec tunnels, CARP-based high availability, VLAN segmentation, and QoS optimization, the organization achieved a resilient and scalable private network. The new infrastructure delivers both operational stability and enterprise-grade security, supporting continued expansion with confidence.
← Back to Case Studies